The Silent Resource Drain
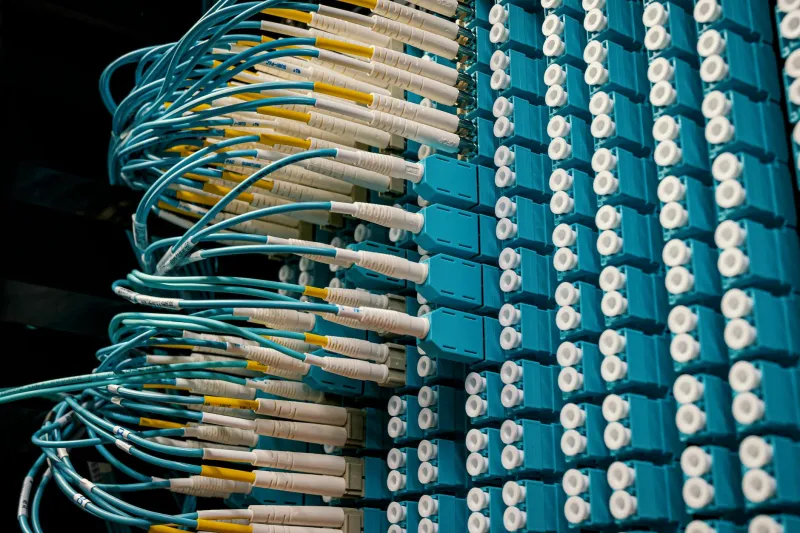
In the depths of UK business server environments, a peculiar phenomenon is quietly unfolding. Applications installed years ago continue to consume CPU cycles, storage space, and memory, despite serving no discernible business purpose. These ghost applications represent one of the most overlooked sources of inefficiency in modern IT infrastructure, yet their impact on both costs and security posture can be substantial.
The problem has reached epidemic proportions across UK enterprises. A recent informal survey of IT departments in London, Manchester, and Edinburgh revealed that the average business server hosts between three and seven applications that nobody can adequately explain or safely remove. These digital phantoms persist not through malice or negligence, but through the accumulated complexity of organisational growth and technological evolution.
Unlike obvious infrastructure waste such as oversized storage allocations or excessive bandwidth provisioning, ghost applications hide in plain sight. They appear in server monitoring dashboards, consume licensing fees, and create potential attack vectors, yet remain invisible to business stakeholders who assume everything running on company servers must serve a legitimate purpose.
The Anatomy of Application Abandonment
Ghost applications emerge through predictable organisational patterns that repeat across industries and company sizes. Understanding these patterns is crucial for UK IT teams seeking to identify and eliminate resource waste from their hosting environments.
Staff turnover represents the most common catalyst for application abandonment. When the marketing manager who championed a particular analytics tool leaves the company, institutional knowledge of that application often departs with them. The software continues running, consuming resources and potentially processing data, but nobody remaining in the organisation understands its purpose or feels confident enough to switch it off.
Mergers and acquisitions create particularly fertile ground for ghost applications. When a Manchester-based logistics company acquires a smaller competitor, the integration process typically focuses on customer databases and core business systems. Secondary applications used by the acquired company for specific operational needs often get overlooked, continuing to operate in their original hosting environment whilst serving no purpose in the combined organisation.
Project abandonment contributes significantly to the ghost application population. Development teams across the UK regularly launch proof-of-concept applications or trial implementations that never progress to full deployment. These experimental systems often remain active on development servers that gradually transition into production environments, creating long-term hosting commitments for short-term projects.
The Hidden Costs of Digital Neglect
The financial impact of ghost applications extends far beyond simple resource consumption. UK businesses hosting these digital derelicts face a complex web of ongoing costs that compound over time and create unexpected budget pressures.
Licensing fees represent the most obvious expense. Software vendors rarely provide automatic termination of unused licences, meaning businesses continue paying annual fees for applications that serve no business function. A typical ghost application might consume £2,000 to £5,000 annually in licensing costs alone, multiplied across multiple abandoned systems in larger organisations.
Resource consumption creates subtler but equally significant costs. Ghost applications compete with active systems for server capacity, potentially triggering premature infrastructure upgrades or forcing businesses to purchase additional hosting resources earlier than necessary. The cumulative effect across multiple abandoned applications can represent 15-20% of total server capacity in severely affected environments.
Security maintenance demands ongoing attention regardless of application utility. Ghost applications require security patches, vulnerability assessments, and monitoring resources equivalent to active business systems. UK IT teams often find themselves allocating significant time and effort to maintaining applications that provide no business value, creating opportunity costs that impact more critical infrastructure projects.
The Security Shadow
Abandoned applications represent a particularly insidious security risk because they combine attractive attack surfaces with minimal oversight. Ghost applications rarely receive the same attention as active business systems, creating potential backdoors that sophisticated attackers can exploit to gain broader network access.
The problem becomes acute when ghost applications contain sensitive data that accumulates over time. A customer relationship management system abandoned after a departmental reorganisation might continue collecting data through automated integrations, creating an unmonitored repository of personal information that violates GDPR compliance requirements.
Outdated software versions compound the security risk significantly. Ghost applications often run on deprecated platforms or use obsolete frameworks that no longer receive security updates. These systems become increasingly vulnerable over time, yet remain connected to business networks where they can serve as entry points for malicious actors seeking to compromise more valuable targets.
Systematic Discovery and Documentation
Effective ghost application hunting requires structured investigation techniques that combine technical analysis with organisational archaeology. UK IT teams need systematic approaches that can reliably identify abandoned systems without disrupting legitimate business operations.
Server monitoring data provides the foundation for ghost application discovery. Applications that show minimal user interaction over extended periods warrant investigation, particularly if their resource consumption patterns suggest automated rather than human activity. Monitoring tools can identify applications that receive no external connections, process no user transactions, or generate no meaningful output over 90-day observation periods.
Financial records offer another valuable discovery vector. Applications that generate ongoing licensing costs but appear in no departmental budgets or business process documentation likely qualify as ghost applications. Cross-referencing software asset management databases with actual server deployments often reveals significant discrepancies that highlight potential abandonment.
Stakeholder interviews remain essential despite their time-intensive nature. Systematically questioning department heads about applications running on business servers frequently reveals knowledge gaps that indicate ghost applications. The key lies in asking specific questions about application purpose, user base, and business impact rather than simply requesting lists of software that departments use.
Safe Decommissioning Strategies
Removing ghost applications requires careful planning to avoid disrupting legitimate business processes that might depend on seemingly abandoned systems. UK businesses need structured decommissioning approaches that minimise risk whilst maximising resource recovery.
Phased shutdown represents the safest decommissioning strategy for most ghost applications. Rather than immediately terminating suspicious systems, IT teams should implement graduated restrictions that test for hidden dependencies. Beginning with read-only access restrictions and progressing through network isolation to complete shutdown allows businesses to identify unexpected connections before permanent removal.
Data preservation protocols ensure compliance with legal and regulatory requirements even when applications appear completely abandoned. UK businesses must maintain appropriate records of data contained within ghost applications, particularly when those systems might have processed personal information or financial data subject to retention requirements.
Rollback procedures provide essential insurance against decommissioning errors. Maintaining complete system backups and documented restoration procedures allows businesses to quickly recover ghost applications that prove essential to business operations despite appearing abandoned during initial investigation.
Building Institutional Memory
Preventing future ghost application accumulation requires systematic changes to how UK businesses document and manage their application portfolios. The most successful organisations implement formal application lifecycle management processes that track systems from initial deployment through eventual decommissioning.
Application ownership registers provide crucial institutional memory that survives staff turnover and organisational changes. These registers should document not only technical specifications but also business justification, user communities, and decommissioning criteria for every application hosted on business infrastructure.
Regular application audits create ongoing opportunities to identify emerging ghost applications before they become entrenched resource drains. Quarterly reviews that combine technical monitoring data with business stakeholder validation can catch abandoned applications whilst institutional memory of their purpose remains accessible.
The ghost application problem represents more than just inefficient resource utilisation. It reflects broader challenges in how UK businesses manage the complexity of modern IT infrastructure. Addressing these digital phantoms requires systematic investigation, careful planning, and ongoing vigilance, but the rewards in terms of cost savings, security improvement, and operational clarity make the effort worthwhile for any business serious about optimising their hosting environment.